Self Service Website
The self service website will allow end users who encounter BitLocker issues to recovery their own BitLocker Recovery Key. The Self Service website is https://mbam.oit.ncsu.edu.
BitLocker can enter into a recovery state for a number of reasons including changes to the BIOS or TPM. For users in the High option, who must use a startup Pin, a lost or stolen Pin may require access to the Recovery Key for the operating system to successfully boot.
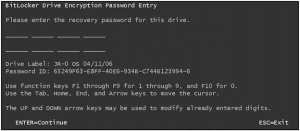
In those events the end user will be presented with a BitLocker Drive Encryption Password Entry screen.
In order to recover the drive the user will need the Password ID.
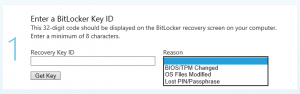
Users will login to the Self Service site using their unityID and password. On the BitLocker Self Service site the users will enter the Password ID as well as a reason for needing the Recovery Key.
The reason has no bearing on the key recovery process but is there for auditing reasons.
If the Password ID can be validated the user will be given the 48-digit Recovery Key that they will need to type in. The Recovery Key is one time use, so a new key will be needed for each recovery event.
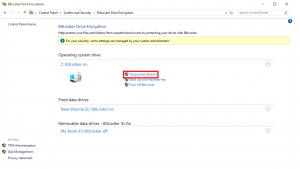
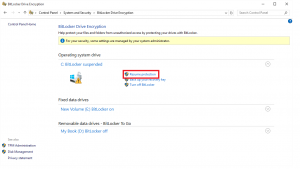
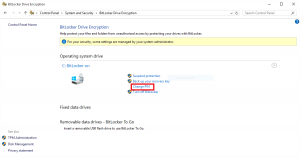
If there were authorized changes made to the BIOS, after the drive is unlocked the changes will have to be “committed”. If not, every time the user reboots they will presented with the BitLocker Drive Encryption Password Entry screen. To commit changes go to the Control Panel -> System and Security -> BitLocker Drive Encryption
Under Operation system drive “Suspend protection”
Administrator credentials will need. Then “Resume protection”
A reboot is not necessary
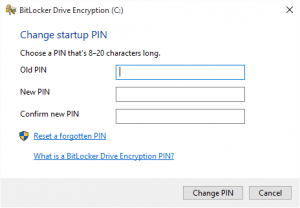
Those users in the High option who have forgotten their Pin can change their Pin in the Control Panel.
Users will be asked for the Current and New Pin